Australian businesses are losing thousands of dollars to malicious ransomware such as Cryptolocker.
In the last year alone, the Australian Cyber Security Centre (ACSC) responded to 2,266 cybersecurity incidents. Of these incidents, the ACSC noted that ransomware attacks were the most serious threats. 33% of businesses paid the ransom, with each breach costing an average of AU$1.25 million.
Regardless of your size, ransomware has the potential to strangle businesses, and smart CFOs and CIOs need to know how to combat this threat.
So let’s start at the beginning.
What is ransomware?
Ransomware is a particular type of malware that infects computer systems and restricts user access. The aim is to trick the user into clicking a link or downloading an infected file, which then installs the malware on the user’s computer.
Once installed, the malware begins to encrypt the user’s files, effectively locking them out of their system. The victim will then receive an on-screen alert, or an email notification, letting them know that their files have been locked and encrypted.
A ransom is then demanded before access to the files is restored, typically in the form of money, information, or cryptocurrency like Bitcoin. If no ransom is forthcoming, the files will be deleted.
And it’s on no small scale, either. In 2020, one local Melbourne business’ files were held to ransom to the tune of $20,000. They didn’t pay—and ended up losing years’ worth of important, irreplaceable information.
In February 2020, an international organisation with an office in Perth had their computer systems locked in a ransomware attack, with the hackers demanding $30 million in ransom.
Ransomware is extortion, plain and simple, undertaken through digital means. And due to the increasingly sophisticated nature of the medium, it’s an insidious threat that needs to be taken seriously.
How is it spread?
Ransomware is typically spread through phishing emails or through drive-by downloads. A drive-by download occurs when a user visits an unsafe site—or, in some cases, even a safe site—and a malicious file automatically downloads itself to your computer. These digital gremlins then spread swiftly throughout your computer, infecting more files, until you receive notification that the attack has occurred.
What is Cryptolocker?
Cryptolocker is a specific piece of ransomware that’s grown in notoriety over recent years. More dangerous than standard ransomware, Cryptolocker doesn’t just go after the files on one drive on your computer. It also affects files that are mapped on drives, like D, E, or F, and can spread to external hard-drives, USBs, or folders on your network or in the Cloud (like Dropbox).
Cryptolocker comes in different variants and is known to spread through social media, such as web-based instant messaging applications. The latest release targets Windows 10—at the moment, Macs are safe.
Impact
Cryptolocker hijacks files, prevents access, and disrupts your normal IT operations. Confidential and proprietary information can be stolen.
Infections by Cryptolocker can have devastating consequences to your organisation, and recovery is usually difficult and costly. You’re dealing with modern-day pirates, but without the luxury of such a strict code of ethics: paying the ransom doesn’t guarantee that the malware infection will be removed or the encrypted files restored.
Solution
With this in mind, the best defence against Cryptolocker is prevention. Here are the steps you can take to give your organisation the best chance of protection against a Cryptolocker attack.
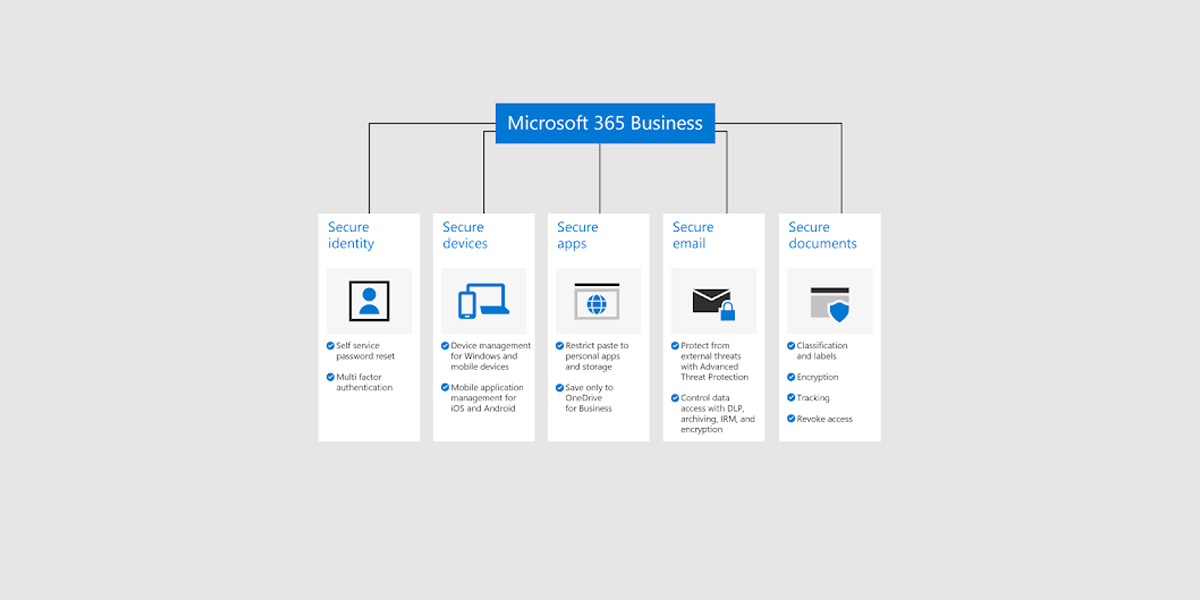
1) Ensure your organisation has a backup and recovery plan for critical information. Make sure your system and files are backed up regularly on both external and internal storage systems that are isolated from your network. By performing regular back-ups to locations removed from your network, should a Cryptolocker attack occur you can roll back your system to the last recent back-up, without losing too much valuable information.
2) Provide thorough ransomware training and education for your staff. Make sure they understand what ransomware is, and what an attack can look like. Give them clear instructions on what to do if they encounter something they think might be a potential ransomware trap.
3) Use whitelisting applications to prevent unapproved software from running.
4) Keep your operating system and software up-to-date with the latest patches.
5) Use the latest anti-virus software.
6) Restrict your users’ ability to install or run unauthorised software applications.
7) Block suspicious emails with attachments.
Most of the time, ransomware attacks are financially motivated.
But the cost to a business runs deeper. Valuable information can be impossible to recreate. Reputational loss can be irrecoverable.
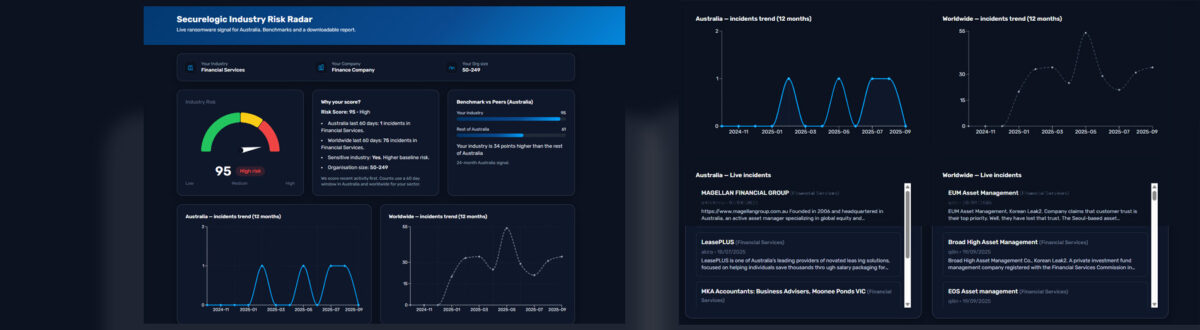
A reliable computer security system can help protect your business from vicious ransomware attacks. If you’re concerned about ransomware, or think you may have been infected, contact Securelogic today.
Source
Australian Competitor and Consumer Association (2017). ‘Malware and ransomware.’ Accessed from: https://www.scamwatch.gov.au/types-of-scams/threats-extortion/malware-ransomware