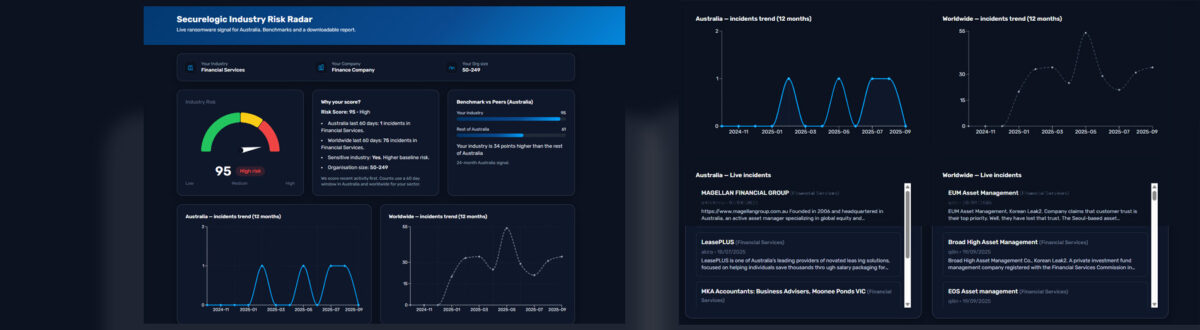
Cyber-attacks continue to grow in complexity and pose significant dangers for businesses across all industries. One cybersecurity incident can result in days of downtime and cost your company hundreds of thousands of dollars. A data breach can also damage your relations with clients and make it difficult to regain public trust.
Looking at different ways to protect your business against these evolving threats is critical for all companies. A ransomware attack can cripple business operations and expose confidential data to the public if you don’t pay the hefty ransom fee. Cybercriminals can also use other methods to target businesses, whether it’s spear-phishing scams to steal user login information or a man-in-the-middle attack (MitM) to intercept confidential data.
Taking additional steps to mitigate the potential impact of a cyber attack is critical in today’s age of digital threats. Investing resources and time into staying proactive against cyber threats can save your business countless expenses and protect your reputation from negative publicity. Working with your in-house IT team or an IT service provider is critical in boosting your cybersecurity operations to stay one step ahead of an ever-changing digital landscape.
Australian Government’s Essential 8
The Australian government released eight different steps to boost cyber security measures for organizations. These steps are also known as the “Essential 8”, as implementing these mitigation strategies can play a vital role in further decreasing the number of cybersecurity incidents in the workplace. Proactively following this guideline will give your business the best protection against cyber threats now and in the future. A partnership with an IT service provider is a great way to implement these strategies to ensure your business continues to stay up to date on the most recent cybersecurity guidelines.
Here is an overview of the Australian Cyber Security Centre’s (ACSC) Essential 8.
1) Essential 8 – Application Control
Application control is also known as “application whitelisting” as it allows the IT team to identify which applications are permitted to operate on a computer or network. One of the main goals of application control is to prevent unsafe applications from deploying malware and causing a cybersecurity incident in the workplace. An IT service provider or your in-house IT team can update this list at any time. Whitelisting can also be implemented in a variety of ways, such as on computers, mobile devices, data hubs, servers, and network equipment.
2) Essential 8 – Patch Applications
Keeping client and server-based applications up to date is critical in staying proactive against cyber threats and software vulnerabilities. Downloading the latest updates for drivers and firmware is also important in reducing the chance of a cybersecurity incident. Turning on automatic updates is a convenient feature, as many employees will delay downloading an update due to time constraints. Besides improving security, application updates can also provide new features and improve performance.
3) Essential 8 – Configure Microsoft Office Macro Settings
Microsoft Office macros can be used to infect a computer with malware. Taking the time to configure these macro settings is important for cyber security. You will need to block macros embedded in documents from any unverified sources, as cybercriminals can easily infect computers by using this method. It’s always a smart idea to only enable the execution of approved macros while restricting security reconfiguration for any macros by a user.
4) Essential 8 – User Application Hardening
User application hardening is another way to limit the functions of an application. Performing this task minimizes the risk of unexpected or malicious activity from applications, which is especially important for cyber security. A few examples of user application hardening includes disabling flash, limiting Java functions, blocking internet ads, and any other unnecessary features on applications or web browsers. Disabling these various features can play a key role in preventing many cyber attacks, as computers are often infected by malware through applications.
5) Essential 8 – Daily Backups
Hardware failure or a cyber attack can result in data loss. Ransomware attacks will also hold data hostage until a ransom fee is paid in cryptocurrency. One of the best ways for your company to stay prepared against these dangers is to enable the creation of daily backups to the cloud. Storing daily backups on the cloud will provide your business with an extra layer of security, as data loss can happen in an almost countless number of ways. Testing these data backups on a regular basis is also a great way to remain proactive to ensure they are readily available if you ever need them during an emergency.
6) Essential 8 – Restrict Administrative Privileges
Cyber attacks will often focus on administrative accounts to gain greater access to the entire computer system and network. These privileged accounts should never be used for checking email, downloading data, or accessing online services due to security concerns. Keeping these administrative accounts to a bare minimum of users is also important in making it difficult for cybercriminals to target these specific accounts. Continually evaluating the privileged rights of employees on an ongoing basis is a good idea to further boost cybersecurity.
7) Essential 8 – Patch Computers
Downloading the latest patches for computers is also important in improving performance and repairing any security vulnerabilities. You can also enable automatic patch updates, which ensures each computer receives an update as soon as possible, instead of relying on each employee to download an update. Patching computers is just another added layer of security against cyber threats.
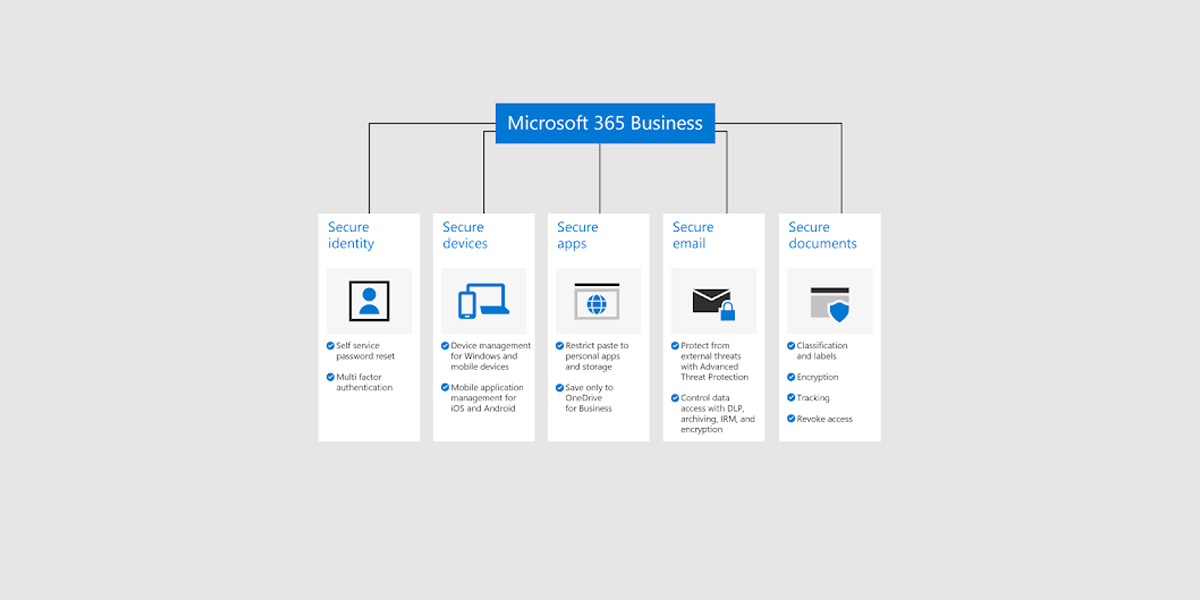
8) Essential 8 – Multi-Factor Authentication
Multi-factor authentication is the process of requiring at least two or more factors to authenticate access credentials for an account. Usually, the first form of authentication is a password. The next form of authentication is often a time-sensitive code sent to an email address or as a text message on a cellphone. Multi-factor authentication plays a key role in keeping accounts secure, as it requires another level of verification instead of solely using a password.
Maturity Levels of Essential 8 Strategies
The ACSC uses three different maturity levels for implementing these Essential 8 strategies, which highlights how prepared a business is to deal with cybersecurity incidents.
Essential 8 Level 1
Only partially implemented the Essential 8 strategies.
Essential 8 Level 2
Mostly implemented the Essential 8 strategies.
Essential 8 Level 3
Fully implemented all of the Essential 8 strategies.
The goal of each business is to reach an Essential 8 Level 3 Maturity for the best protection against all types of cyber threats in the workplace. While the Essential 8 system was initially created for government agencies, it also plays a key role in providing businesses small and large with an added level of security against cybersecurity incidents.
Cyber Security Essential 8 – What Does It Mean for Business?
Taking all of these different IT security steps will greatly reduce the risk of a cyber incident impacting your business. Following these detailed recommendations will also make it easier for your business to recover and continue your daily operations if you are ever the victim of a cyber attack. While following these steps requires a significant investment of time for your IT department or IT provider, it’s well worth the effort. These strategies are now simply part of doing business to help you navigate today’s technology landscape and offer you the best protection available.